easyRSA
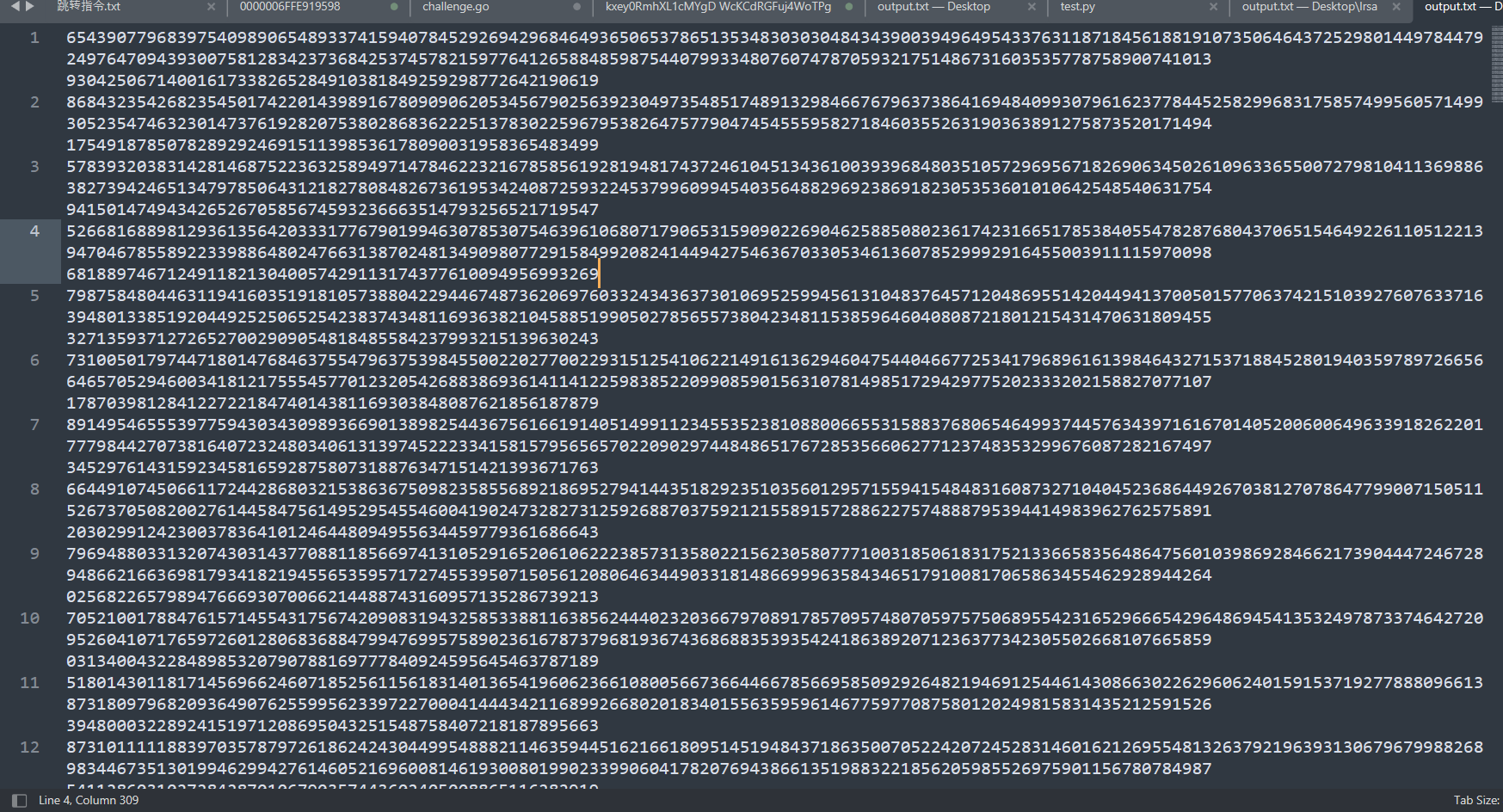
打开发现有多个N
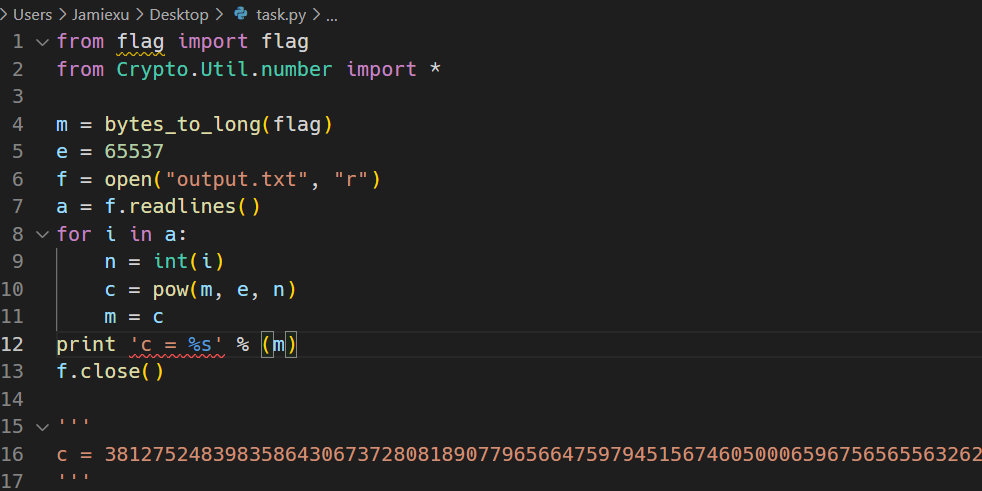
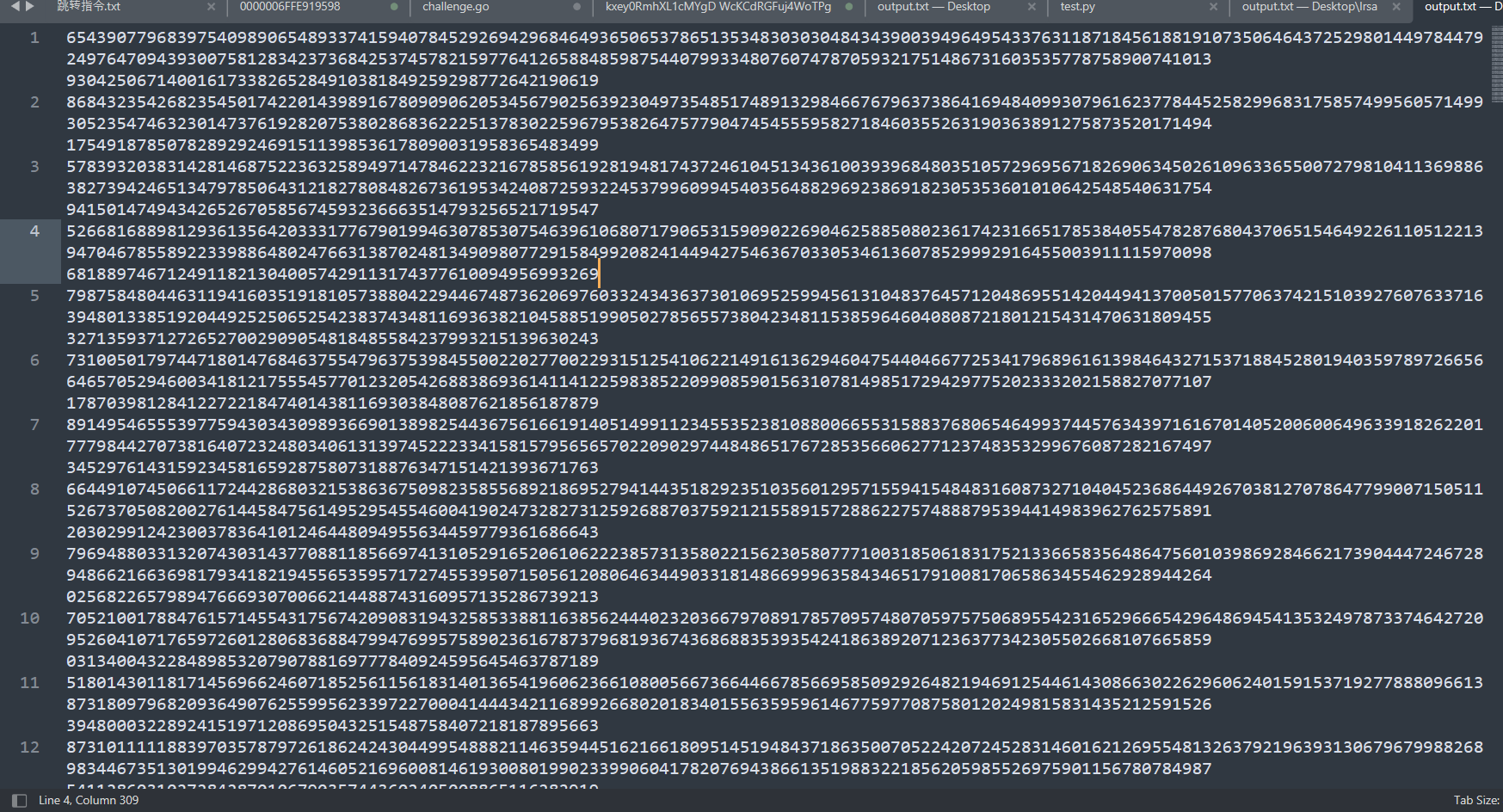
判断是否是使用了公有的素数,尝试使用欧几里得辗转相除分解出公有的素数
确实是使用了公有的素数,直接用n整除common(共同素数)得到另一个素数。
根据公式
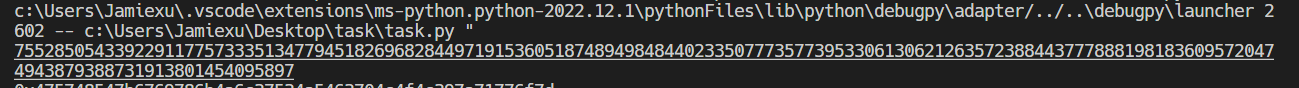
phi = (q -1)*(p - 1),求出phi使用gmpy2求出模逆元d
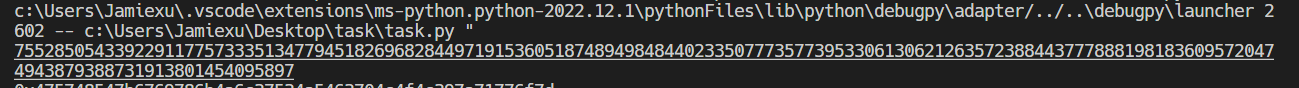
最后循环解密即可
1 | # from flag import flag |
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来源 Jamie793’ S Blog!
评论
打开发现有多个N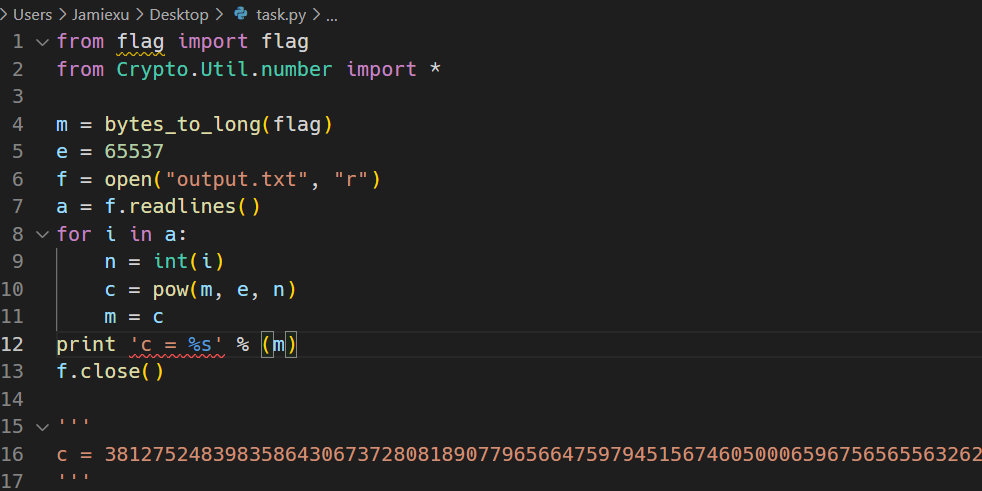
判断是否是使用了公有的素数,尝试使用欧几里得辗转相除分解出公有的素数
确实是使用了公有的素数,直接用n整除common(共同素数)得到另一个素数。
根据公式phi = (q -1)*(p - 1),求出phi
使用gmpy2求出模逆元d
最后循环解密即可
1 | # from flag import flag |